Boost Scoring is a technique used by the SamurAI platform which improves the ability to find Advanced Persistent Threats (APTs) by using a methodology which helps to link seemingly unrelated events allowing the platform to determine where a set of events becomes notable enough to warrant investigation as a threat.
This is done by using the ability to identify suspicious activities using the combined insights offered by multiple enrolled sources, irrespective of technology type or vendor. This enables detection using activities and events that normally would not be of a significant interest by themselves. When seen in combination however they represent individual aspects of a threat. Boost scoring provides a method to link these events and strengthen their relevance when they are combined.
By grouping activities and events on a user and entity basis and Mitre tactic basis, Boost scoring enables identification of suspicious behaviors which are identified via combined insights. The Boost score increases over time providing more accurate confidence and threat severity scoring for each group over time.
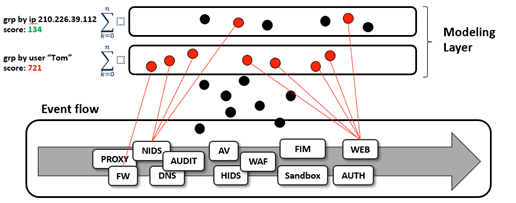
Figure 1: Boost scoring
By keeping the Group state for a long period of time (typically over 60 days) SamurAI is able to detect evasive threats that have stayed dormant for a longer period of time after the initial breach by linking additional events which can be linked to the initial breach attempt.
Once a Boost score reaches a predetermined level it will be used to generate an alert which is presented to SOC analysts. This helps to suppress single indicators from raising alerts, and rather permits the gathering of evidence until a confidence threshold is reached where the raising of an alert is justified.
This technique enables detection of dormant threats and slow-moving attacks (a traditional evasion technique). Suspicious activities are assessed in their entirety regardless of threat severity, time or log source.
Simply put, Boost scoring helps to find the balance between too many alerts (false positives) and too few alerts (false negatives) and in that process selecting the activity which is of real importance in identifying the activity of threat actors.