Overview
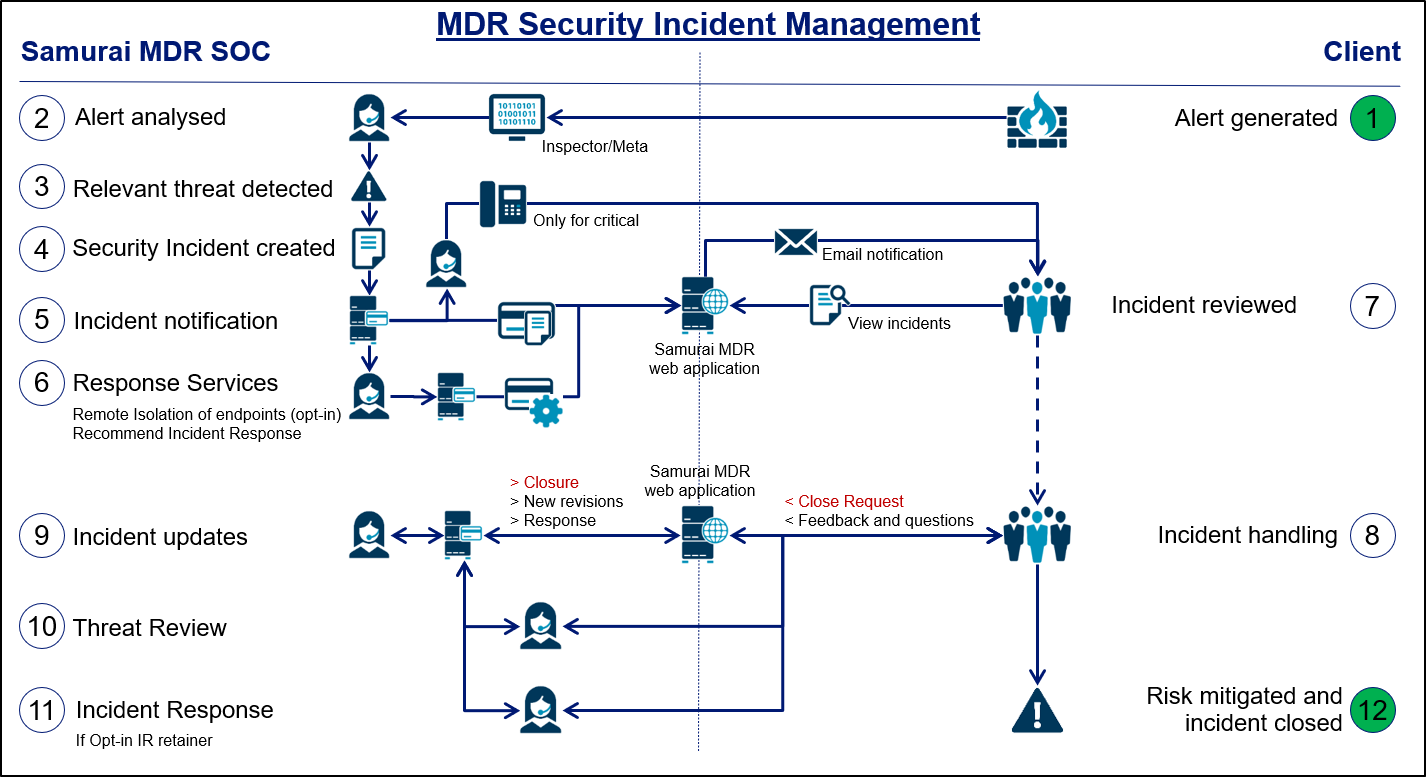
The MDR Security Incident Management process is designed to address reported threats that pose a risk to a client’s environment and to ensure appropriate handling. When the Security Operations Center (SOC) create a Security Incident, it will remain open until the client reports back that the threat had been handled, risk mitigated and closure request submitted.
The more information included in a Security Incident, the easier it will be for a client’s security staff to understand and mitigate the threat, therefore the SOC create a detailed Security Incident viewable within the SamurAI Portal and downloadable in PDF format as required. The SOC also recommend you provide feedback of your incident handling as this could improve future security incidents from the SOC and your own handling of them.
Below is a description of how the SOC performs Security Incident Management when relevant threats are detected and how the Security Incident life-cycle is managed.
Security Incident life-cycle
The Security Incident Management process starts with a security detection (alert) made by the SamurAI platform (Real-time engine or Hunting engine) or third party technology integrated with the SamurAI platform. In all cases, the alert is presented to the the Analyst in the SamurAI platform. Another possible trigger for the Security Incident management process could relate to a known high risk global Security Incident or threat, for example Log4shell or SolarWinds. In this instance, the Analyst conducts Retroactive Hunting in available telemetry data to search for indicators of compromise (IOCs) and determine if a client has been affected by the newly discovered global threat.
Once the Analyst receives an alert, they will start to analyze the threat through an investigation process that includes reviewing AI/ML correlations and threat hunting across all telemetry data and older Security Incidents. In some cases, the Analyst will also try to recreate the threat in the SOC malware lab.
The analysis phase can be time-consuming, but the purpose is to find attack vectors to first verify how the attack has affected the client and how the threat can be mitigated. The more detail known about a threat, the easier it will be to mitigate. However, if the SOC observes that the threat is actively damaging client systems or leaking client data, an initial and expedited Security Incident will be created to inform the client so that client assets can be protected. The SOC will then update the initial Security Incident with all needed threat details.
Security Incident Management
When a new Security Incident is created it will be made available within the SamurAI Portal and an automated email notification is sent to predefined email addresses (collected during the MDR onboarding phase). The email will contain key information such as severity, title, reference ID and a link to the Security Incident within the SamurAI Portal. The initial Security Incident Status is set to Awaiting feedback. If the Security Incident severity is critical, the SOC will also call the client.
When creating the Security Incident, the SOC may perform remote isolation of infected client endpoints using the client’s Endpoint Detection and Response (EDR) platform. The SOC will also include a recommendation whether the client should engage your Incident Response Team (either you have an internal team, NTT is providing or a 3rd party). If further remediation is required the client can also engage the NTT Incident Response Team.
Once the client is informed by a notification email (or telephone call if severity is critical), the Security Incident will enter the handling phase.
The SOC will also include recommendation (actions) for the client to perform. Additional questions can be asked by the client in the Security Incident Situation Room communication channel (Click to read more) Type feedback or comments/questions, in the communications channel and click ‘Send message’.
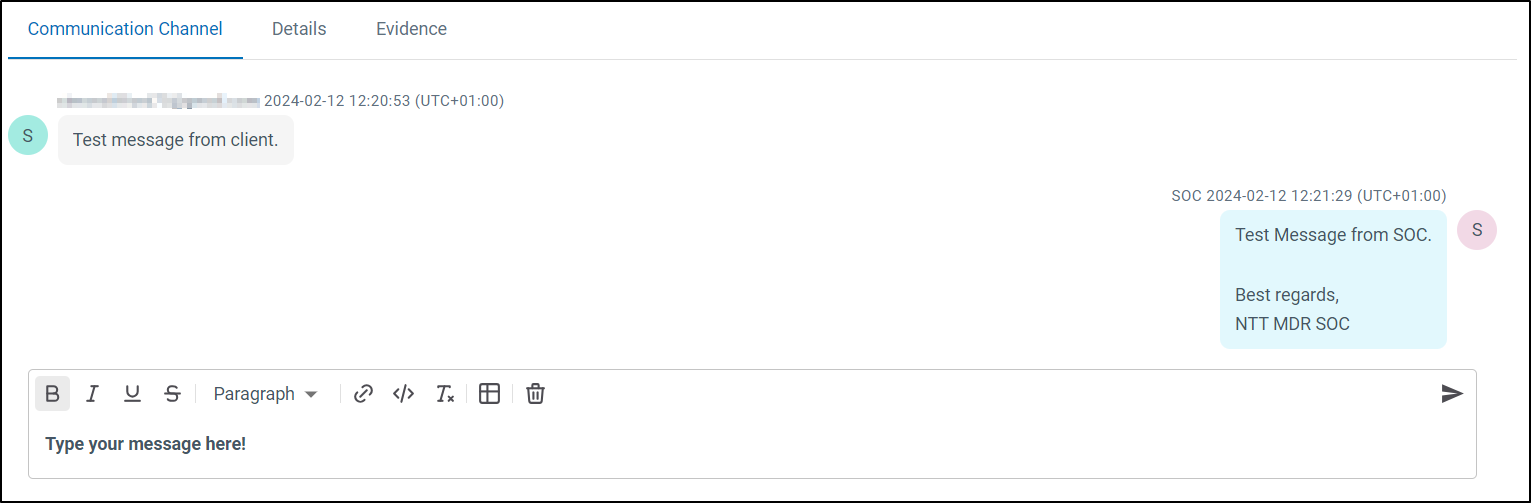
Once the client clicks ‘Send message’, the Security Incident status is updated to Awaiting SOC, meaning the next action is on the SOC. The SOC will respond to your question or feedback. You may still add feedback and questions even if the status is Awaiting SOC and next actions will remain with the SOC.
It is important to ensure that any critical or high severity Security Incidents progress towards closure, therefore you are advised to keep the SOC updated and respond in a timely manner when the status is Awaiting feedback.
As long as the SOC is working on a response to your questions, the Security Incident status will remain as Awaiting SOC. When the SOC responds, the status will be updated to Awaiting feedback. If the SOC detects that a new or existing threat re-emerges or there is new vital information, the Security Incident will be updated, a new revision created and a notification emailed to you.
Closure
When the risk has been mitigated or the client has accepted the risk (e.g. managing the threat), the client can request the Security Incident to be closed via the Security Incident Situation Room. This decision is based on the client’s assessment that sufficient action to mitigate the risk has been taken and is now comfortable with closure of the Security Incident. In the event the SOC receive feedback to close the request during an open investigation, confirmation of the request will be included in the ticket details.
Non-closure
If the SOC does not receive a closure request from the client, the security incident will be kept active and in an Awaiting feedback status. The SOC will present and go through all of the non-closed security incidents during the regular Threat Review Meetings. This to ensure client handling of all reported threats and risks, If the SOC has received no feedback, this could mean that the threat is still present and active, despite being reported months ago.